Many business owners and property managers assume standard WPA2 encryption fully protects their wireless networks. Recent research reveals sophisticated attacks bypass client isolation even on encrypted networks, exposing sensitive data. This guide explains modern wireless security threats facing Stockholm SMBs and properties, compares WPA2 versus WPA3 protocols, and shows how professional Ubiquiti Unifi installation creates genuinely secure networks in 2026.
Table of Contents
- Understanding Wireless Network Vulnerabilities In 2026
- Comparing WPA2 And WPA3: Why Upgrading Matters
- Harnessing WiFi 7 And Modern Standards For Secure High-Speed Networks
- Practical Wireless Security For SMBs And Properties In Stockholm
- Secure Your Wireless Network With Expert Ubiquiti Unifi Installation In Stockholm
- Wireless Network Security Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Modern attacks bypass standard protections | AirSnitch exploits architectural flaws to defeat client isolation without breaking WPA2 encryption. |
| WPA3 offers critical security improvements | Enhanced handshake protocols and Protected Management Frames prevent password guessing and spoofing attacks. |
| WiFi 7 mandates strong security features | Enforces WPA3 and PMF on 6GHz bands whilst delivering 1.5–3Gbps throughput for high-speed secure networks. |
| Professional installation maximises protection | Proper segmentation, VLAN configuration, and expert network design prevent architectural vulnerabilities. |
Understanding wireless network vulnerabilities in 2026
Wireless networks face sophisticated threats that standard encryption alone cannot prevent. The AirSnitch attack demonstrates how attackers exploit fundamental architectural weaknesses in WiFi design.
Researchers found all tested routers vulnerable to at least one AirSnitch attack exploiting Group Temporal Keys. This technique bypasses client isolation by abusing how wireless networks share encryption keys amongst connected devices. Unlike traditional attacks that break encryption, AirSnitch works within the encryption framework itself.
The implications for SMBs and property networks are serious:
- Attackers can intercept cookies and session tokens from other users on the same network
- DNS poisoning redirects legitimate traffic to malicious servers
- Sensitive business data transfers between devices become visible to attackers
- Guest network isolation fails, exposing corporate resources
WPA2’s well-documented KRACK vulnerability allows attackers to intercept and decrypt data by manipulating the four-way handshake. This attack works even when you use strong passwords and proper configuration. The vulnerability exists in the protocol itself, not in implementation mistakes.
“Client isolation on wireless networks provides a false sense of security when architectural flaws allow GTK abuse to bypass access point restrictions entirely.”
Encryption protects data in transit but cannot compensate for flawed network architecture. Many SMB wireless networks rely solely on WPA2 encryption whilst neglecting proper segmentation, device access controls, and protocol updates. This creates multiple attack vectors that determined cybercriminals readily exploit.
Understanding why secure WiFi protects your business requires recognising that modern threats target protocol weaknesses and architectural gaps rather than brute-forcing passwords. Legacy security approaches leave Stockholm businesses and properties vulnerable despite appearing properly configured.
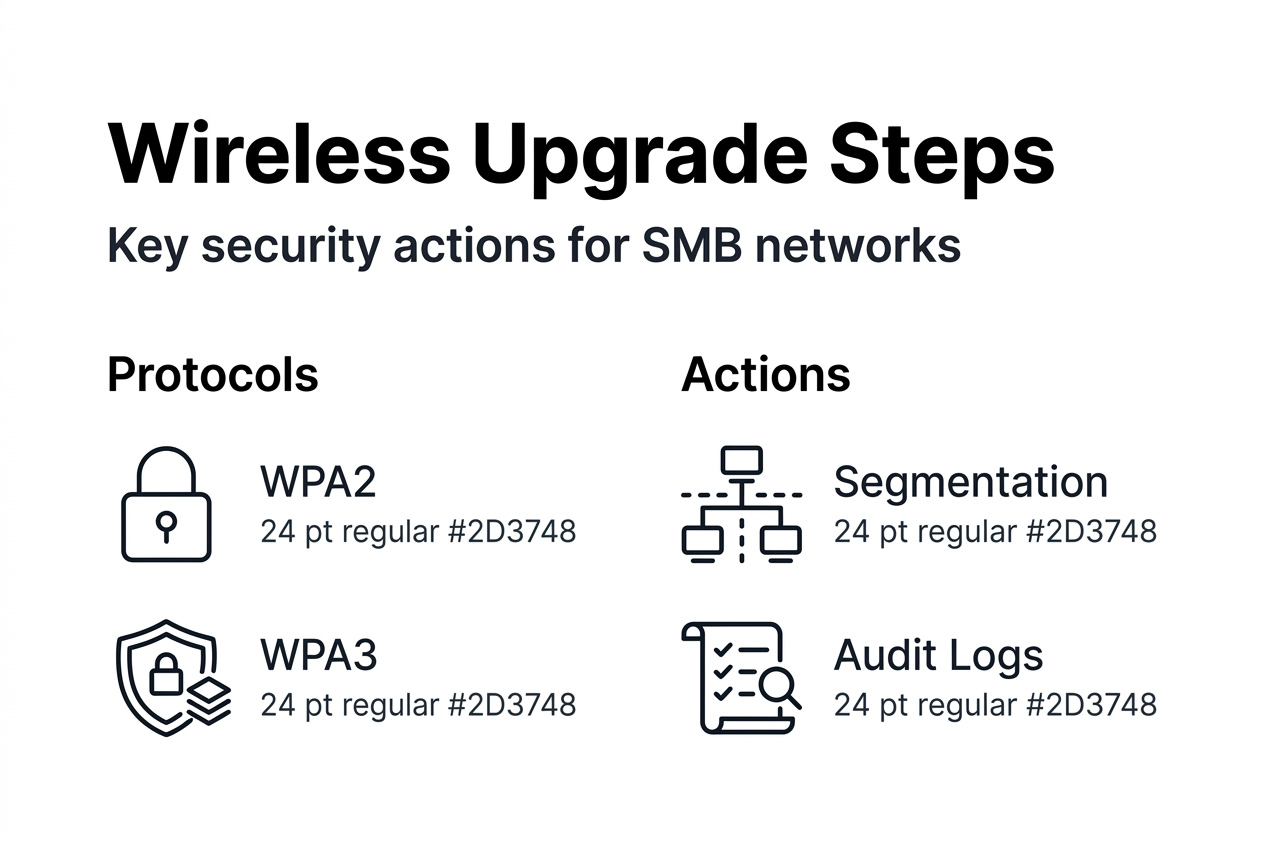
Comparing WPA2 and WPA3: why upgrading matters
WPA3 represents a fundamental security overhaul rather than incremental improvement. Understanding these differences helps SMBs make informed decisions about network upgrades.
WPA2 uses AES encryption with a pre-shared key model vulnerable to offline dictionary attacks. If someone captures your four-way handshake, they can attempt unlimited password guesses without connecting to your network. KRACK exploits allow attackers to decrypt traffic by forcing key reinstallation.
WPA3 delivers complete security improvements over WPA2 through Simultaneous Authentication of Equals. This protocol prevents offline password guessing by requiring active participation from the access point for each attempt. Attackers must interact with your network directly, making brute-force attacks detectable and rate-limited.
| Feature | WPA2 | WPA3 |
|---|---|---|
| Handshake protocol | Four-way handshake (vulnerable to KRACK) | SAE (prevents offline attacks) |
| Password protection | Vulnerable to dictionary attacks | Forward secrecy protects past sessions |
| Management frame protection | Optional | Mandatory on 6GHz |
| Public network security | No individualised encryption | Opportunistic Wireless Encryption |
Protected Management Frames prevent deauthentication attacks and other spoofing techniques. On 6GHz WiFi bands, PMF becomes mandatory, eliminating an entire class of disruption attacks that plague WPA2 networks. This proves particularly valuable for property networks serving multiple tenants or businesses hosting guest access.
WPA3-first network design significantly reduces risk from legacy device vulnerabilities. Rather than allowing old devices to force your entire network down to WPA2, create separate SSIDs for different security tiers. Modern devices connect via WPA3 whilst legacy equipment uses isolated WPA2 networks with restricted access.
Pro Tip: Configure Ubiquiti Unifi networks with WPA3-only access for business devices and a separate WPA2/WPA3 transition SSID for guest access. This ensures maximum security for sensitive operations whilst maintaining compatibility.
Migrating to WPA3 should integrate with holistic security upgrades including secure WiFi essentials for SMEs such as VLAN segmentation, strong authentication, and centralised management. The protocol upgrade provides maximum benefit when combined with proper network architecture.
Harnessing WiFi 7 and modern standards for secure high-speed networks
WiFi 7 transforms wireless networking by combining unprecedented speed with mandatory strong security. For Stockholm SMBs and properties, this represents an opportunity to address performance and security simultaneously.
WiFi 7 throughput ranges 1.5–3Gbps with 2×2 clients whilst enforcing WPA3 and PMF on 6GHz bands. This eliminates the security compromises often made for legacy compatibility. The 6GHz spectrum provides clean channels free from interference whilst mandating the strongest available protection.
Mandatory WPA3 on 6GHz eliminates older protocol vulnerabilities entirely. Devices cannot connect using WPA2 or earlier standards, closing legacy gaps that attackers exploit. This architectural decision by the WiFi Alliance ensures new spectrum benefits security alongside performance.
| WiFi Generation | Typical Speed | Security Requirement | Best Use Case |
|---|---|---|---|
| WiFi 5 (802.11ac) | 300–900Mbps | WPA2 minimum | Legacy device support |
| WiFi 6 (802.11ax) | 600–1.2Gbps | WPA3 recommended | Mixed environments |
| WiFi 6E | 900–1.8Gbps | WPA3 mandatory (6GHz) | High-density deployments |
| WiFi 7 (802.11be) | 1.5–3Gbps | WPA3+PMF mandatory (6GHz) | Future-proof installations |
Migrating to WiFi 7 should be treated as a security project, not merely a performance upgrade. The transition provides opportunity to redesign network architecture, implement proper segmentation, and establish strong access controls that protect against current and emerging threats.
Best practices for secure WiFi 7 migration include:
- Conduct network audit identifying all connected devices and their security capabilities
- Design VLAN structure separating corporate, guest, and IoT traffic
- Configure separate SSIDs for different security tiers and user groups
- Implement certificate-based authentication for business-critical access
- Establish monitoring and alerting for unusual connection patterns
Pro Tip: When deploying WiFi 7 access points, disable legacy protocol support on 6GHz radios entirely. Use 2.4GHz and 5GHz bands with WPA2/WPA3 transition mode only for devices that absolutely require it.
Ubiquiti Unifi systems support these modern standards through flexible network configurations and centralised management. Professional installation ensures proper radio planning, channel selection, and security policy implementation that maximises both performance and protection.
Phased migration allows businesses to adopt WiFi 7 strategically. Start with high-security areas requiring fastest speeds, then expand coverage whilst maintaining legacy support where necessary. This approach balances security improvements with operational continuity.
Exploring secure WiFi solutions for SMBs helps identify the right balance of performance, security, and compatibility for your specific environment and device mix.
Practical wireless security for SMBs and properties in Stockholm
Translating technical knowledge into actionable security requires understanding how attacks exploit real-world network configurations and implementing defences that address root causes.
Professional network installation ensures proper segmentation and controlled device access. GTK abuse represents an architectural vulnerability that access point restrictions cannot prevent. Only network-level segmentation through VLANs and firewall rules provides effective protection.
Implement these security measures for Stockholm SMB and property networks:
- Segment networks by trust level – Create separate VLANs for corporate devices, guest access, IoT equipment, and building management systems. Configure firewall rules preventing cross-VLAN traffic except where explicitly required.
- Deploy WPA3 with PMF – Enable WPA3-Personal or WPA3-Enterprise on all SSIDs serving modern devices. Activate Protected Management Frames to prevent deauthentication and disassociation attacks.
- Isolate legacy devices – Place WPA2-only devices on dedicated SSIDs with restricted network access. Regularly audit these devices and upgrade or replace equipment that cannot support WPA3.
- Use strong authentication – Implement WPA3-Enterprise with RADIUS authentication for corporate access. Require unique credentials rather than shared passwords that enable offline attacks.
- Monitor network activity – Configure logging and alerting for unusual connection patterns, repeated authentication failures, and unexpected device types joining the network.
- Maintain current firmware – Establish procedures ensuring access points, switches, and security gateways receive regular updates addressing newly-discovered vulnerabilities.
Guest and IoT device segmentation proves particularly critical:
- Guest networks should have no access to internal resources
- IoT devices require internet access but rarely need local network connectivity
- Building management systems need isolated networks with strict access controls
- Printers and shared devices should authenticate users before granting access
Pro Tip: Configure Ubiquiti Unifi guest portals with time-limited access codes that expire automatically. This prevents old credentials from providing ongoing network access after guests depart.
Regular security reviews identify emerging risks. Quarterly audits should examine connected devices, review access logs, verify firewall rules remain appropriate, and confirm firmware versions include latest security patches.
Following a comprehensive network installation checklist ensures critical security steps receive proper attention during deployment. Professional installers understand how architectural decisions affect long-term security and can design networks that resist current and future threats.
Consider managed WiFi services for SMBs lacking in-house technical expertise. Professional monitoring, regular updates, and expert support maintain robust security without requiring dedicated IT staff. Learning how to install Unifi networks properly from the start prevents costly security remediation later.
Strong passwords alone cannot compensate for architectural weaknesses. Combining WPA3 protocols with proper network segmentation, device isolation, and professional configuration creates defence-in-depth that protects Stockholm businesses and properties from sophisticated wireless attacks.
Secure your wireless network with expert Ubiquiti Unifi installation in Stockholm
Protecting your business or property requires more than purchasing quality equipment. Professional installation ensures wireless networks implement the security practices explained throughout this guide.
Our Stockholm-based team specialises in Ubiquiti Unifi solutions combining modern security protocols with reliable performance. We design segmented networks preventing GTK abuse and other architectural attacks whilst maintaining the flexibility SMBs need. Centralised management through Unifi Controller simplifies ongoing security maintenance and monitoring.
Experienced technicians understand how network architecture affects security. We implement VLAN segmentation, configure WPA3 with Protected Management Frames, and establish access controls that protect against current threats. Our network installation approach follows proven checklists ensuring critical security steps receive proper attention.
Using a comprehensive Ubiquiti Unifi installation checklist helps avoid common pitfalls that create vulnerabilities. Professional network installation in Stockholm provides the foundation for reliable, secure wireless connectivity that grows with your business.
Ready to implement genuinely secure wireless networking? Boka Tid
Contact us directly:
Email: kontakt@natverkstekniker.se
Wireless network security frequently asked questions
What makes WPA3 more secure than WPA2?
WPA3 uses Simultaneous Authentication of Equals preventing offline password attacks that compromise WPA2 networks. Forward secrecy protects past sessions even if current passwords become compromised, whilst mandatory Protected Management Frames on 6GHz bands prevent spoofing attacks.
How does AirSnitch affect my wireless network security?
AirSnitch exploits how WiFi networks share Group Temporal Keys amongst connected devices, bypassing client isolation without breaking encryption. Attackers can intercept cookies, perform DNS poisoning, and access traffic between other network users, making proper VLAN segmentation essential.
Is professional installation necessary for Ubiquiti Unifi networks?
Professional installation ensures proper network architecture preventing GTK abuse and other vulnerabilities that configuration alone cannot address. Expert technicians implement VLAN segmentation, configure appropriate security protocols, and establish access controls that maximise protection whilst maintaining usability.
Can WiFi 7 improve my network security and speed?
WiFi 7 delivers 1.5–3Gbps throughput whilst mandating WPA3 and Protected Management Frames on 6GHz bands. This eliminates legacy protocol vulnerabilities, provides clean spectrum free from interference, and ensures new deployments use the strongest available security from the start.
How often should I review and update my wireless security?
Conduct quarterly security audits examining connected devices, reviewing access logs, and verifying firmware currency. Immediately update access points and security gateways when vendors release patches addressing newly-discovered vulnerabilities. Establish automated monitoring alerting you to unusual connection patterns requiring investigation.